Cross-site request forgery, also known as one-click attack or session riding and abbreviated as XSRF or CSRF, is a type of malicious exploit of a website where unauthorized commands are transmitted from a user that the web application trusts. Unlike cross-site scripting (XSS), which exploits the trust a user has for a particular site, CSRF exploits the trust that a site has in a user's browser.
SAP expects it's clients to send a valid CSRF token in the HTTP header X-CSRF-Token with every request, except for GET and OPTIONS. If you don't, you will receive an error response with the status code 403 and the text "CSRF token validation failed" as body.
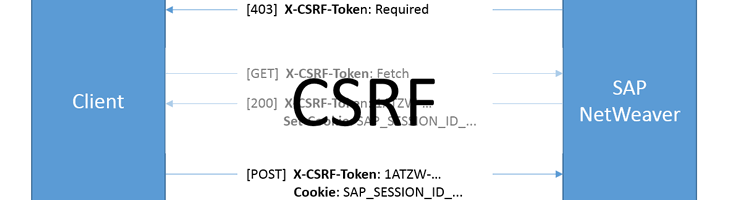
Here is, how the tokens work:
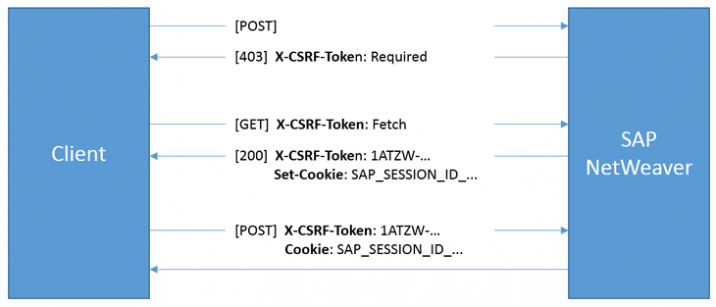
SAP CSRF protection: request flow
In a nutshell, you must request a token with a separate special request first. This token will be valid for the lifetime of your SAP session. When the session ends, you must request a new token.
You can request as many tokes as you need within one session. Thus, you can either request a token for every request, or save it with your SAP session ID somewhere in client storage an reuse it until you get a new session id with one of the requests.
If you use the OData model, built into SAP UI5, this is all done automatically. But if you want to use OData or other NetWeaver webservices with another Javascript framework or an external application, you will have to do it manually:
1) Fetch a CSRF-token
Send a GET-request to your target webservice with the appropriate Authorization header, no cookies and the X-CSRF-Token header set to Fetch. Here is, how this looks in Postman.
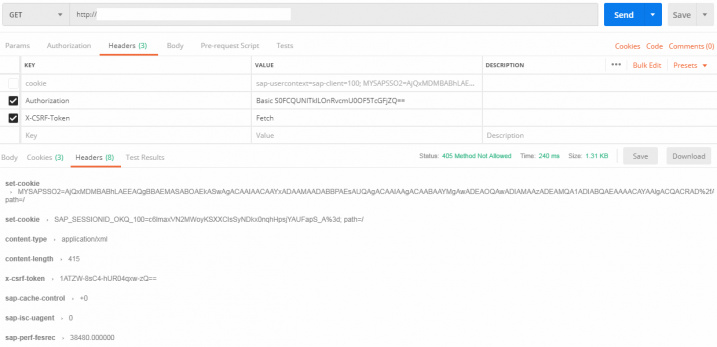
Fetching an CSRF-token from SAP Netweaver
The response may even be an error (as in the screenshot above), but it will contain the needed information in it's headers:
X-CSRF-Tokenwill contain the newly issued tokenSet-Cookiewill contain our SAP session ID
2) Send the CSRF-Token with every request
Now, you can send your payload-requests with the two headers from the initial CSRF-fetch-request. Here is, how this would look in Postman:
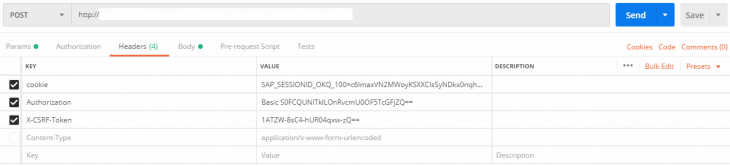
Sending POST requests with CSRF-tokens to SAP Netweaver
If your session or token expire, you will get a 403-error again. Just repeat the steps above and you are good to go again!